How to File a Cyber Crime Complaint in Pakistan (2026): Complete Step-by-Step Guide
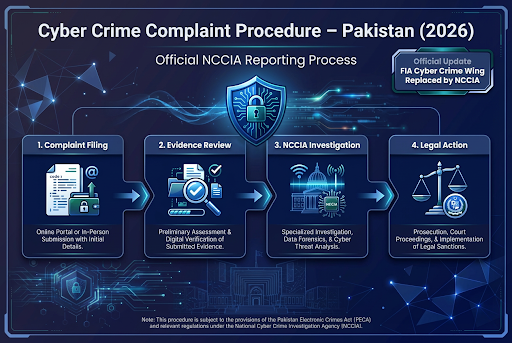
Important Update: NCCIA Now Handles All Cybercrime Complaints
As of February 2026, Pakistan's cybercrime investigations are no longer handled by the Federal Investigation Agency (FIA) Cyber Crime Wing. The Government of Pakistan established the National Cyber Crime Investigation Agency (NCCIA) as an independent, autonomous authority replacing the FIA's cybercrime functions entirely.
If you're searching for "FIA cyber crime complaint" or "how to report to FIA," this guide will direct you to the correct current procedures under NCCIA while explaining what changed and why it matters for victims of cyber crime.
Understanding Pakistan's Cybercrime Investigation Authority
The Transition from FIA to NCCIA
In practice, when victims searched "FIA cyber crime complaint" or tried contacting the FIA Cyber Crime Wing (CCW) before April 2025, they reached the National Response Centre for Cyber Crime (NR3C) operating under FIA supervision. That structure no longer exists.
On May 3, 2024, the government formally established NCCIA under Section 51 of the Prevention of Electronic Crimes Act (PECA) 2016, though full operational transition occurred in April 2025. All cybercrime personnel, cases, investigations, and complaint mechanisms transferred from FIA to this new independent agency.
From a procedural standpoint, this matters because:
- FIA no longer investigates cybercrimes. Complaints submitted to old FIA channels may face delays or confusion.
- NCCIA operates independently with its own complaint portals, helplines, and investigation procedures.
- Legal authority remains under PECA 2016, but enforcement mechanisms now rest with NCCIA rather than FIA.
Courts typically require victims to follow proper complaint procedures. Misdirecting complaints to defunct FIA cybercrime channels could prejudice your case timeline and evidentiary record.
What Is Cyber Crime Under Pakistani Law?
Cyber crime encompasses criminal activities committed using digital devices, computer networks, or the internet. The Prevention of Electronic Crimes Act (PECA) 2016 defines specific offenses that fall under NCCIA's investigative jurisdiction:
Section 20 - Cyber Harassment: Includes threats, intimidation, blackmail, or offensive content transmitted electronically with intent to coerce or harass. Courts typically examine whether the accused intended to cause psychological harm or fear.
Section 21 - Misuse of Personal Images: Unauthorized distribution, transmission, or display of someone's photographs or videos, particularly when done to harm reputation or cause distress. This provision frequently applies in revenge pornography cases and image-based harassment.
Section 22 - Electronic Fraud: Fraudulent schemes conducted through digital means, including fake investment platforms, phishing scams, online impersonation for financial gain, and unauthorized electronic fund transfers.
Section 24 - Cyberstalking: Persistent online harassment creating reasonable fear for personal safety. This differs from Section 20 harassment by requiring a pattern of repeated unwanted contact.
Section 36 - Unauthorized Access: Gaining access to information systems, databases, or accounts without authorization. This covers hacking, password cracking, and unauthorized system intrusions.
Additional offenses under PECA include spreading false information (Section 20), unauthorized interception of communications (Section 25), malicious code distribution (Section 34), and cyberterrorism (Section 10).
In practice, many cybercrimes involve multiple PECA violations simultaneously. An online fraud scheme might include unauthorized access to banking credentials (Section 36), electronic fraud (Section 22), and identity theft.
Types of Cybercrime Cases NCCIA Handles
From a procedural standpoint, NCCIA investigates the following categories of digital offenses:
Financial Cybercrimes
These constitute the majority of complaints NCCIA receives. According to government data presented to the National Assembly in January 2026, NCCIA received over 150,000 cybercrime complaints in 2025, with 81,996 related to financial fraud specifically.
Common financial cybercrime patterns include:
-
Fake investment schemes: Fraudsters create counterfeit trading platforms or cryptocurrency investment websites promising unrealistic returns. Victims transfer funds that disappear once scammers achieve their targets. In June 2025, NCCIA arrested suspects involved in a Rs. 20 billion fake trading scheme operating in Multan. \
-
Banking and payment fraud: Unauthorized transactions through compromised bank accounts, mobile banking apps, ATM cards, or mobile wallet services (Easypaisa, JazzCash, etc.). These often result from phishing attacks or malware infections. \
-
Online shopping scams: Fake e-commerce websites collecting payments without delivering products, or selling counterfeit goods misrepresented as genuine. \
-
Job offer frauds: Scammers impersonating legitimate companies, collecting "processing fees" from job seekers who never receive actual employment. \
Social Media Crimes
Social media platforms provide venues for various criminal activities NCCIA investigates:
-
Fake profiles and impersonation: Creating fraudulent accounts using someone's photographs, name, or personal information to damage reputation or commit fraud. Courts typically consider the impersonation's intent - whether defamatory, fraudulent, or harassing. \
-
Account hacking: Unauthorized access to Facebook, Instagram, Twitter, TikTok, or other social media accounts. In 2025, NCCIA received 2,974 complaints specifically regarding WhatsApp account hacking. \
-
Defamation and character assassination: Publishing false, offensive content about individuals with intent to damage reputation. These cases require balancing free speech considerations against legitimate privacy and dignity protections. \
Cyber Harassment and Gender-Based Digital Violence
Harassment cases constitute a significant portion of NCCIA's workload, particularly those targeting women and minors:
-
Blackmail using intimate images: Threatening to distribute private photographs or videos unless victims comply with demands (typically financial or sexual). This combines elements of harassment (Section 20), misuse of personal images (Section 21), and potentially extortion under general criminal law. \
-
Persistent unwanted contact: Repeated messages, calls, or social media interactions despite clear rejection. Cyberstalking cases require documented evidence of pattern and persistence. \
-
Online abuse and threats: Direct threats of violence, rape, or harm transmitted electronically. Courts typically examine whether threats created reasonable fear in victims and whether accused had apparent means to execute threats. \
From a procedural standpoint, harassment complaints require substantial documentary evidence - screenshots with visible dates and times, message headers showing sender information, and consistent chronological records.
Hacking and Unauthorized Access
Technical cybercrimes involving unauthorized system access:
-
Email account hacking: Unauthorized access to personal or business email accounts, often used for subsequent fraud or information theft. \
-
Website defacement: Altering website content without authorization, often for political messaging or vandalism. \
-
Data theft and breaches: Unauthorized extraction of confidential information from databases, corporate systems, or personal devices. \
-
Malware distribution: Creating or spreading viruses, ransomware, trojans, or other malicious software. \
How to File a Cybercrime Complaint with NCCIA: Step-by-Step Process
Method 1: Online Complaint Through NCCIA Portal
The most accessible method for most victims involves filing complaints through NCCIA's official online portal.
Step 1: Access the Official Complaint Portal
Navigate to complaint.nccia.gov.pk [blocked] (the current official NCCIA complaint portal). Avoid third-party websites claiming to process complaints - these may be phishing attempts themselves.
Previously, victims used complaint.fia.gov.pk [blocked] when FIA handled cybercrimes. That portal may still exist but redirects to NCCIA or no longer processes new cybercrime complaints. Always use the official NCCIA portal to ensure proper complaint registration.
Step 2: Select Crime Category
NCCIA's portal categorizes complaints by offense type:
- Cyber Crime (general digital offenses)
- Online Fraud
- Cyber Harassment
- Social Media Crimes
- Hacking/Unauthorized Access
- Identity Theft
- Other Electronic Crimes
Selecting the appropriate category ensures your complaint reaches the correct investigation unit within NCCIA. If your situation involves multiple offense types, choose the most serious or primary violation.
Step 3: Provide Complete Personal Information
The complaint form requires:
- Full Name (as per CNIC)
- CNIC Number (mandatory for Pakistani citizens; passport number for foreign nationals)
- Complete Address (include city, postal code)
- Mobile Number (must be active for investigation updates)
- Email Address (for official correspondence and complaint tracking)
In practice, investigators use this contact information for verification, additional information requests, and case updates. Providing accurate details prevents delays when NCCIA needs to reach you for statement recording or evidence submission.
Step 4: Describe the Incident Comprehensively
This section proves critical for investigation initiation. Courts typically require clear, detailed factual allegations to establish prima facie evidence of offense.
Your complaint description should include:
What happened: Describe the cybercrime incident specifically. Instead of "someone hacked my account," write "On January 15, 2025, I discovered unauthorized access to my Gmail account (username@gmail.com). The intruder changed my password, sent emails to my contacts requesting money, and accessed confidential business documents."
When it occurred: Provide specific dates and times when possible. For ongoing harassment, note when it began and when most recent incident occurred.
Who committed it: Identify the perpetrator if known - name, phone number, email address, social media username, account details. If identity is unknown, describe identifying information available (profile names, account numbers, transaction IDs).
How it affected you: Explain the harm - financial losses (specific amounts), reputational damage, emotional distress, business disruption, safety concerns.
Common mistakes include vague descriptions lacking specific facts. "Someone is harassing me online" provides insufficient detail. "User 'FakeProfile123' has sent threatening messages to my Instagram account daily since January 1, 2025, including threats to harm my family if I don't send money" gives investigators actionable information.
Step 5: Upload Supporting Evidence
Evidence quality significantly impacts investigation success. NCCIA accepts digital evidence in various formats:
Screenshots: Capture complete images showing:
- Offensive messages or posts with visible dates, times, and sender information
- Fake profiles using your photographs or information
- Fraudulent websites or transactions
- Threatening emails with full headers
From a procedural standpoint, ensure screenshots include contextual information. A cropped image showing only message text without sender details or timestamps may lack evidentiary value.
Communication records:
- Email exchanges (export as PDF or EML files including headers)
- SMS/WhatsApp message logs (export chat history)
- Social media conversation threads
- Call logs showing harassing phone numbers
Financial documentation:
- Bank statements showing unauthorized transactions
- Payment receipts for fraudulent purchases
- Transaction confirmations from mobile wallets
- Investment documents for fraud schemes
Additional evidence:
- Voice recordings (if harassment occurred via calls)
- Video evidence (if applicable)
- Witness statements (written declarations from others who observed the crime)
File formats accepted typically include JPEG, PNG, PDF, MP3, MP4. Maximum file size limits apply (usually 5MB per file, with multiple uploads permitted).
Critical evidence preservation rule: Never delete original evidence from your devices. NCCIA's digital forensics team may need to examine original files, message metadata, or device logs during investigation. Deleting evidence, even inadvertently, can compromise case prosecution.
Step 6: Submit Complaint and Record Reference Number
After reviewing all information, submit the complaint form. The system generates a unique complaint reference number (typically alphanumeric code like CCR-2025-12345).
Record this reference number immediately. You'll need it for:
- Tracking complaint status
- Providing additional information
- Following up on investigation progress
- Referencing the case in any legal proceedings
NCCIA sends confirmation to your registered email address. If you don't receive confirmation within 24 hours, verify email correctness and check spam folders.
Method 2: WhatsApp Complaint Submission
NCCIA provides WhatsApp-based complaint registration for accessibility, particularly for victims uncomfortable with computer-based portals.
Contact NCCIA through their official WhatsApp helpline (number available on nccia.gov.pk [blocked]website). Send message stating:
"I want to file a cybercrime complaint regarding [brief incident description]."
NCCIA staff will guide you through information requirements and evidence submission process. This method allows sending screenshots and documents directly through WhatsApp.
From a procedural standpoint, WhatsApp complaints receive the same investigation priority as online portal submissions. However, online portal complaints may process faster due to automated data entry systems.
Method 3: In-Person Complaint at NCCIA Office
For complex cases, sensitive situations, or when victims prefer face-to-face interaction, visiting NCCIA offices directly remains an option.
NCCIA Headquarters National Police Foundation Building, 2nd Floor Sector G-10/4, Islamabad Phone: 051-9106691 (updated from previous FIA helpline 1991)
NCCIA Circle Offices operate in major cities:
- Lahore: House No. B-8, G Block, Main Boulevard, Gulberg-II
- Karachi: (Contact NCCIA headquarters for current Karachi circle address)
- Rawalpindi: House No 162/2, Punj Sarrki, Near Shell Petrol Pump, Adam Jee Road, Sadar
- Faisalabad: Zia Town, Street No 2, East Canal Road, Near Kashmir Pul
- Quetta: Banglow No. 105, Tajikabad, Adjacent to Spirit School, Main Killi Shabo Road
- Multan, Gujranwala, Peshawar, and other cities also maintain circle offices
For current addresses and contact information, visit nccia.gov.pk/contact [blocked] or call the main helpline 1799 (NCCIA's national cybercrime helpline number).
What to bring for in-person complaints:
- Original CNIC (photocopies accepted)
- Written complaint application stating all incident details
- Printed evidence (screenshots, bank statements, etc.)
- Digital evidence on USB drive or memory card
- Contact information for receiving updates
In practice, officers at NCCIA circles assist with complaint drafting if victims need help formulating written applications. Don't let uncertainty about proper legal language prevent you from reporting - officers can guide you through documentation requirements.
After Filing Your Complaint: What Happens Next
Complaint Acknowledgment and Registration
Upon submission through any channel, NCCIA:
- Issues complaint reference number for tracking
- Conducts preliminary review to verify jurisdiction and offense type
- Assigns to relevant investigation unit based on crime category
- Contacts complainant if additional information needed
This preliminary process typically takes 3-7 working days, though urgent cases (threats to life, ongoing financial fraud) may receive immediate attention.
Investigation Process
NCCIA's investigation typically follows these stages:
Initial Evidence Analysis: Digital forensics team examines submitted evidence - analyzing screenshots for authenticity, tracing IP addresses, examining email headers, reviewing transaction records.
Technical Investigation: For cases requiring deeper analysis:
- Requesting information from social media platforms (Facebook, WhatsApp, Instagram) regarding account ownership, IP logs, or message metadata
- Coordinating with banks to trace fraudulent transactions
- Working with telecom companies to identify phone numbers or SIM card registration details
- Analyzing devices (if accused's equipment seized) for incriminating data
Suspect Identification and Verification: Using technical evidence, investigators identify perpetrators. This may involve:
- Tracing payment accounts to bank records and CNIC information
- Linking social media accounts to registered phone numbers
- Using digital forensics to uncover account creation details
Statement Recording: NCCIA calls complainants to record formal statements under oath. Courts typically require sworn statements as foundational evidence for prosecution. Ensure your oral statement aligns with written complaint details.
Confrontation and Arrest: If sufficient evidence exists, NCCIA issues arrest warrants for accused individuals. In practice, many cyber harassment cases resolve through mediation before trial when accused agree to cease offensive behavior and remove defamatory content.
Expected Timeline
Case resolution timelines vary significantly based on complexity:
- Simple harassment cases with clear evidence: 4-8 weeks for initial investigation and potential arrest
- Financial fraud requiring inter-bank coordination: 3-6 months for complete investigation
- International elements (perpetrators abroad): 6-12 months or longer, requiring cooperation through INTERPOL or bilateral agreements
- Complex hacking cases needing advanced forensics: 6-12 months
Common delays occur when:
- Complainants provide incomplete evidence initially
- Social media platforms or banks delay responding to information requests
- Suspects cannot be located or evade arrest
- Technical analysis requires specialized expertise
Tracking your complaint status through the reference number helps identify if investigation has stalled and whether follow-up action is needed.
Critical Evidence Requirements for Successful Prosecution
Courts typically require admissible electronic evidence meeting legal standards. Understanding evidentiary requirements improves investigation outcomes.
Screenshot Best Practices
From a procedural standpoint, proper screenshots should:
Include complete context: Capture entire screen showing browser address bar (for websites), application name, date/time, and sender information - not just the offensive content.
Preserve metadata: When possible, use screenshot tools that embed capture date/time in image metadata. Some courts accept metadata as evidence of timing.
Maintain chronological order: Number sequential screenshots (Image_1, Image_2, etc.) showing conversation flow or incident progression.
Avoid alterations: Never edit screenshots to "clarify" content. Courts may reject edited images as unreliable. If something is unclear in original, explain it in your written statement rather than altering evidence.
Communication Record Preservation
For harassment cases involving ongoing communication:
Export complete conversations: Many platforms allow exporting entire chat histories. Full exports provide better context than selective screenshots.
Preserve original messages: Don't delete messages even after reporting. WhatsApp, email, and social media platforms store message data that investigators can request during investigation.
Document blocking actions: If you blocked the harasser, note when and document any attempts to contact you through alternative accounts.
Financial Fraud Documentation
For fraud complaints:
Transaction details: Bank statement entries, transaction IDs, payment confirmations, cryptocurrency wallet addresses.
Communication with fraudsters: Messages or calls where fraudulent scheme was pitched, promised returns discussed, payment instructions given.
Platform information: Website addresses of fraudulent sites (accessed while investigators can still analyze them), app names, company names used by scammers.
Loss quantification: Exact amounts lost with dates. Courts require specific monetary damage amounts for restitution orders.
Your Rights During NCCIA Investigation
Understanding your legal rights prevents potential abuse during investigation process.
Right to Confidentiality
PECA includes victim protection provisions. NCCIA must maintain confidentiality of:
- Your personal information (addresses, contact details)
- Sensitive evidence (particularly intimate images in harassment cases)
- Your identity in certain situations where disclosure might cause further harm
In practice, courts typically order in-camera proceedings (closed courtroom) for cases involving Section 21 violations (intimate image misuse) to protect victim privacy.
Right to Legal Representation
You may engage a lawyer at any investigation stage. Legal counsel helps ensure:
- Your statements are accurately recorded
- Your interests are protected during evidence submission
- Procedural requirements are properly followed
- You understand legal developments as investigation progresses
Particularly in complex cases or when you receive NCCIA notices for additional information, legal guidance proves valuable.
Right to Updates on Investigation Progress
Complainants can request investigation status updates through:
- Calling NCCIA helpline with your reference number
- Emailing helpdesk@nccia.gov.pk (updated from previous nr3c.gov.pk email)
- Visiting relevant circle office
While investigators cannot disclose sensitive operational details that might compromise investigation, they should provide general status information - whether case remains under investigation, whether arrests occurred, or whether case has been forwarded for prosecution.
Protection from Harassment
Some victims face retaliation after filing complaints - threats to withdraw complaints, pressure from accused's family members, or attempts at intimidation.
Report any such incidents immediately to NCCIA. Witness intimidation and attempting to influence criminal proceedings constitute separate criminal offenses. NCCIA can provide protective measures for victims facing threats.
Common Mistakes to Avoid When Filing Cybercrime Complaints
From practical legal experience, these errors frequently delay or weaken cases:
Waiting Too Long to Report
Digital evidence degrades over time. Social media posts get deleted, accounts deactivated, messages disappear, security camera footage overwrites. Courts have limitation periods for certain offenses.
Report cybercrimes as soon as they occur. Even if you're gathering evidence, file an initial complaint establishing the timeline, then supplement with additional evidence as it becomes available.
Deleting Evidence
Never delete offensive messages, posts, or accounts thinking "I've already screenshot them." Investigators often need:
- Email headers (showing routing information and IP addresses)
- Message metadata (transmission times, geolocation data)
- Account activity logs (accessible through original platforms)
These elements may prove crucial for suspect identification but become inaccessible once you delete original evidence.
Taking Matters Into Your Own Hands
Victims sometimes retaliate by hacking the harasser's account, posting public accusations, or engaging in counter-harassment. This creates legal problems:
- Your retaliatory actions may constitute separate PECA violations
- Evidence you obtained through illegal hacking becomes inadmissible
- Accused can file counter-complaints, complicating your original case
Report to authorities and let investigators handle evidence collection through legal channels.
Providing False Information
Exaggerating facts, fabricating evidence, or filing false complaints constitutes a criminal offense under Section 182 PPC (giving false information to public servant). Courts severely penalize false cybercrime reports.
If you realize some information in your complaint was incorrect, immediately contact NCCIA to provide corrections. Honest mistakes corrected promptly differ significantly from deliberate falsehoods discovered during investigation.
Neglecting Follow-Up
Filing a complaint doesn't guarantee automatic resolution. Periodically check investigation status, respond promptly to any NCCIA requests for additional information, and appear when called for statement recording.
Cases often stall because complainants become unresponsive, assuming investigation continues independently.
Special Considerations for Different Types of Cyber Crime
Harassment Cases Involving Women and Minors
Pakistani courts recognize heightened vulnerability of women and children to cyber harassment. PECA Section 20 explicitly mentions enhanced protections for these groups.
From a procedural standpoint:
- Female complainants can request female officers for statement recording
- Parents or legal guardians file complaints on behalf of minor victims
- Courts may order expedited investigation for cases involving minors or serious threats
- Protective orders can prohibit accused from contacting victim during proceedings
Women Development Department in Punjab also operates cybercrime complaint cells in coordination with NCCIA, providing additional support channels for female victims.
Financial Fraud Across International Borders
Many online frauds involve perpetrators operating from other countries - particularly investment scams, romance frauds, and fake job offers originating abroad.
NCCIA coordinates with international law enforcement through:
- INTERPOL channels for arrest and extradition
- Mutual Legal Assistance Treaties (MLATs) with other countries
- Direct agency-to-agency cooperation for cybercrime investigation
However, international cases face practical limitations. Perpetrators in jurisdictions without extradition agreements with Pakistan may evade prosecution. NCCIA can still pursue local accomplices or intermediaries operating within Pakistan.
For cross-border fraud:
- Document all international communication (email addresses, phone numbers with country codes, website registrations)
- Preserve transaction routing information showing money flows
- Note any Pakistani-based elements (bank accounts, phone numbers, accomplices)
Corporate/Business Cyber Crime
Businesses facing cyber attacks, data breaches, or corporate account compromise should:
Segregate affected systems immediately: Prevent further data exfiltration or damage while preserving forensic evidence.
Engage cybersecurity professionals: For incident response and evidence collection. Professional forensic analysis strengthens NCCIA investigation.
File complaints promptly: Many businesses delay reporting fearing reputational damage. Early reporting enables faster response and may prevent ongoing breaches.
Coordinate with NCCIA investigators: Provide system logs, network traffic analysis, employee access records as requested.
NCCIA's corporate cybercrime units handle sophisticated attacks requiring advanced technical expertise - different from typical harassment complaints.
The Role of PECA 2016 in Cybercrime Prosecution
Understanding the Prevention of Electronic Crimes Act helps victims comprehend their legal protections and potential case outcomes.
Key PECA Provisions Affecting Complainants
Section 31 - Offenses by Companies: When cybercrimes are committed by corporate entities, company directors and officers face personal liability. This provision helps victims pursue fraudulent businesses, not just individual employees.
Section 33 - Extraterritorial Jurisdiction: PECA applies to offenses committed by:
- Pakistani citizens anywhere in the world
- Anyone committing offenses from within Pakistan
- Anyone committing offenses targeting persons or systems in Pakistan
This broad jurisdiction means NCCIA can investigate even if perpetrator operates abroad, though enforcement challenges exist.
Section 37 - Protection of Victims and Witnesses: Courts must ensure victim and witness safety, confidentiality where appropriate, and protection from intimidation.
Penalties Under PECA
Understanding potential sentences helps victims assess case seriousness:
- Cyber harassment (Section 20): Up to 3 years imprisonment and/or fine up to Rs. 1 million
- Misuse of personal images (Section 21): Up to 3 years imprisonment and/or fine up to Rs. 1 million
- Electronic fraud (Section 22): Up to 3 years imprisonment and/or fine up to Rs. 1 million
- Cyberstalking (Section 24): Up to 3 years imprisonment and/or fine up to Rs. 1 million
- Unauthorized access (Section 36): Up to 3 years imprisonment and/or fine up to Rs. 1 million
- Cyberterrorism (Section 10): Up to 14 years imprisonment
Courts may impose both imprisonment and fines. Victims can also pursue civil damages separately for financial losses or reputational harm.
Alternatives and Complementary Actions to NCCIA Complaints
While NCCIA handles criminal investigation, victims have additional legal options:
Civil Litigation for Damages
File civil defamation suits or claims for damages in appropriate courts. Civil litigation provides:
- Monetary compensation for losses
- Injunctive relief (court orders prohibiting further harassment or defamatory content)
- Faster resolution timeline in some cases
Civil and criminal proceedings can proceed simultaneously. Consult legal counsel regarding civil remedies appropriate for your situation.
Platform-Level Reporting
Social media platforms have internal complaint mechanisms:
- Facebook/Instagram: Report offensive content or fake profiles through platform reporting tools
- Twitter/X: File abuse reports for harassing accounts
- YouTube: Report harassment, privacy violations, or offensive content
- WhatsApp: Report spam or abusive contacts
Platform companies may remove content, suspend accounts, or provide account information to law enforcement during NCCIA investigation. Platform reporting complements (but doesn't replace) NCCIA complaints for cases involving criminal violations.
Pakistan Telecommunication Authority (PTA) Complaints
For certain telecommunication-related issues, PTA accepts complaints:
- Spam messages or calls
- Misuse of telecommunication services
- Blocking objectionable online content
PTA can issue directions to service providers and coordinates with NCCIA for criminal matters.
Technology Tools Supporting Cyber Crime Prevention
While reporting mechanisms are essential after crimes occur, preventive measures reduce victimization risk.
Digital Security Best Practices
Courts typically consider whether victims exercised reasonable precaution when assessing cases. While victim-blaming is inappropriate, basic security measures strengthen your position:
Strong passwords: Use unique, complex passwords for each account. Password managers help maintain security without memorizing dozens of combinations.
Two-factor authentication: Enable 2FA on banking, email, and social media accounts. This prevents unauthorized access even if passwords are compromised.
Regular software updates: Keep operating systems, apps, and antivirus software current. Many cyberattacks exploit known vulnerabilities in outdated software.
Suspicious link avoidance: Don't click links in unexpected emails or messages. Phishing attacks distribute malware or steal credentials through disguised links.
Privacy settings: Configure social media privacy controls limiting who can view personal information, contact you, or tag you in content.
Evidence Preservation Tools
For victims experiencing ongoing harassment:
Screenshot applications: Tools like Greenshot, Snipping Tool, or mobile screenshot functions preserve visual evidence with timestamps.
Email archiving: Export important emails to local storage (PST files for Outlook, MBOX for Gmail) creating backups independent of email provider.
Cloud storage: Securely back up evidence to cloud services (Google Drive, Dropbox, OneDrive) preventing loss if devices are damaged or seized.
Screen recording: For dynamic content (social media stories, temporary messages), screen recording software captures evidence before it disappears.
Legal Technology for Cybercrime Documentation
Platforms like Legal Sparrow provide resources helping victims understand legal rights, document evidence systematically, and prepare comprehensive complaints. While such platforms cannot replace official NCCIA complaint procedures, they offer educational support helping victims navigate complex cybercrime reporting requirements.
Legal-tech tools can assist with:
- Understanding which PECA provisions apply to specific situations
- Organizing evidence chronologically and categorically
- Drafting clear, factual incident descriptions
- Knowing what information NCCIA investigators need
These resources complement official complaint channels, ensuring victims approach reporting process with proper preparation and understanding.
Frequently Asked Questions About Cybercrime Complaints in Pakistan
Q: Should I file with NCCIA or FIA for cyber crime complaints in 2025?
File with NCCIA. The Federal Investigation Agency no longer handles cybercrime investigations after April 2025. All cybercrime complaints now go to the National Cyber Crime Investigation Agency, an independent authority established specifically for digital crimes.
Attempting to file through FIA channels may result in delays or your complaint being redirected to NCCIA, wasting critical time in time-sensitive cases.
Q: What is NCCIA's helpline number?
NCCIA operates helpline number 1799 for general cybercrime assistance and the office number 051-9106691 for specific complaint follow-up. Previous FIA Cyber Crime Wing helpline (1991) is no longer active for cybercrime matters.
Q: How long does NCCIA take to resolve cybercrime cases?
Investigation timelines vary based on case complexity. Simple harassment cases with clear evidence may resolve within 4-8 weeks. Complex financial fraud requiring inter-bank coordination can take 3-6 months or longer. International cases involving perpetrators abroad may take 6-12 months.
Courts recognize that digital forensics and technical investigation require time. However, you can expedite your case by providing complete evidence initially and responding promptly to any NCCIA requests for additional information.
Q: Can I file a cybercrime complaint anonymously?
No. NCCIA requires complainant identification through CNIC verification for several reasons:
- Courts need complainant testimony for prosecution
- False complaint protection (preventing abuse of cybercrime laws)
- Investigation follow-up and statement recording
However, PECA includes confidentiality provisions protecting victim identities from public disclosure in certain cases, particularly those involving Section 21 violations (intimate image misuse).
Q: What if the cybercriminal is unknown?
File the complaint detailing all available information - usernames, account handles, phone numbers, email addresses, transaction details. NCCIA's technical investigation capabilities can often identify perpetrators from digital footprints even when victims don't know their real identities.
Provide every identifying detail available:
- Complete URLs of fake profiles or fraudulent websites
- Email addresses (including display names)
- Phone numbers (even if unregistered)
- Payment account details (bank accounts, mobile wallet numbers)
- IP addresses (if visible in message headers)
NCCIA coordinates with internet service providers, banks, and platform companies to trace these identifiers to actual individuals.
Q: Does filing a complaint guarantee prosecution?
No. After investigation, NCCIA determines whether sufficient evidence exists for prosecution. Some complaints may not proceed if:
- Evidence is insufficient to establish criminal offense
- Perpetrator cannot be identified despite investigation efforts
- The matter falls outside PECA jurisdiction (civil dispute rather than criminal offense)
However, even if formal prosecution doesn't occur, investigation often results in content removal, account suspension, or cease-and-desist outcomes resolving the immediate problem.
Q: Can I withdraw my cybercrime complaint?
Technically, cybercrime cases are state matters - once NCCIA begins investigation, the state prosecutes based on public interest, not solely complainant wishes. However, in practice:
- Courts consider complainant cooperation essential for harassment cases
- Many cases resolve through mediation before trial
- Complainant testimony proves critical for conviction
If circumstances change (matter resolved privately, mistaken identity discovered), inform NCCIA immediately through proper channels rather than simply abandoning the complaint. Unexplained withdrawal may prejudice future complaints if further incidents occur.
Q: What happens if I file a false cybercrime complaint?
Filing false complaints constitutes a criminal offense under Section 182 PPC (providing false information to public servant) and Section 182 (a) PPC (false information to prevent public servant from duty). Penalties include imprisonment up to six months and/or fine.
NCCIA's investigation verifies complaint authenticity. Deliberate falsehoods discovered during investigation result in counter-prosecution against false complainants.
However, honest mistakes differ from deliberate fabrication. If you realize some complaint details were incorrect, immediately notify NCCIA with corrections. Courts distinguish between good-faith errors and malicious false reporting.
Q: Can businesses file cybercrime complaints?
Yes. Businesses experiencing cyber attacks, data breaches, corporate account compromise, intellectual property theft, or defamation can file NCCIA complaints. Authorized company representatives (directors, legal officers) file on behalf of the business entity.
Corporate cybercrime complaints require:
- Company registration documents
- Authorization letter designating person filing